The shift from gray-zone shadow warfare to direct, state-on-state kinetic exchange between Iran and Israel marks the dissolution of the "campaign between the wars" doctrine. This transition is not merely a localized escalation but a massive stress test of two diametrically opposed military philosophies: the high-cost, high-precision integrated air defense (IAD) model versus the low-cost, high-volume saturation model. Understanding the current instability requires moving beyond headlines of "tension" and instead quantifying the structural components of this conflict—specifically the cost-exchange ratio, the technical limitations of interception, and the shifting definition of "red lines" in a post-April 2024 reality.
The Architecture of Saturation vs. Interception
The tactical reality of this conflict is governed by the physics of offensive saturation and the economics of defensive attrition. Iran’s military strategy relies on the deployment of tiered delivery systems—unmanned aerial vehicles (UAVs), cruise missiles, and ballistic missiles—designed to overwhelm defensive radars through sheer volume and staggered arrival times.
The Cost-Exchange Asymmetry
A fundamental bottleneck in prolonged conflict is the radical disparity in the "per-shot" cost.
- The Offensive Variable: Shahed-series loitering munitions cost approximately $20,000 to $50,000. Even medium-range ballistic missiles (MRBMs) such as the Fattah or Kheibar Shekan, while more expensive, are mass-produced using established industrial pipelines.
- The Defensive Variable: An Arrow-3 interceptor, the top tier of Israel’s multi-layered defense, is estimated to cost between $2 million and $3.5 million per unit. Even the short-range Iron Dome Tamir interceptors cost roughly $40,000 to $50,000—often equal to or more than the target they are destroying.
This creates a scenario where the defender "wins" every tactical engagement by successfully intercepting the threat but "loses" the economic war of attrition. If an aggressor can force the expenditure of 300 interceptors using 300 low-cost drones, the defender’s strategic depth is depleted faster than their industrial base can replenish it.
The Triad of Iranian Delivery Systems
To analyze the threat profile, one must deconstruct the three distinct flight envelopes utilized in recent exchanges. Each serves a specific function in the "saturation ladder."
- Loitering Munitions (UAVs): These function as "electronic sponges." Their slow flight speed (under 200 km/h) makes them easy to detect, but their purpose is to force the activation of fire-control radars and the expenditure of surface-to-air missiles (SAMs), clearing a path for faster assets.
- Cruise Missiles: These offer a low-altitude, terrain-following profile. By staying below the radar horizon for as long as possible, they minimize the reaction time for point-defense systems.
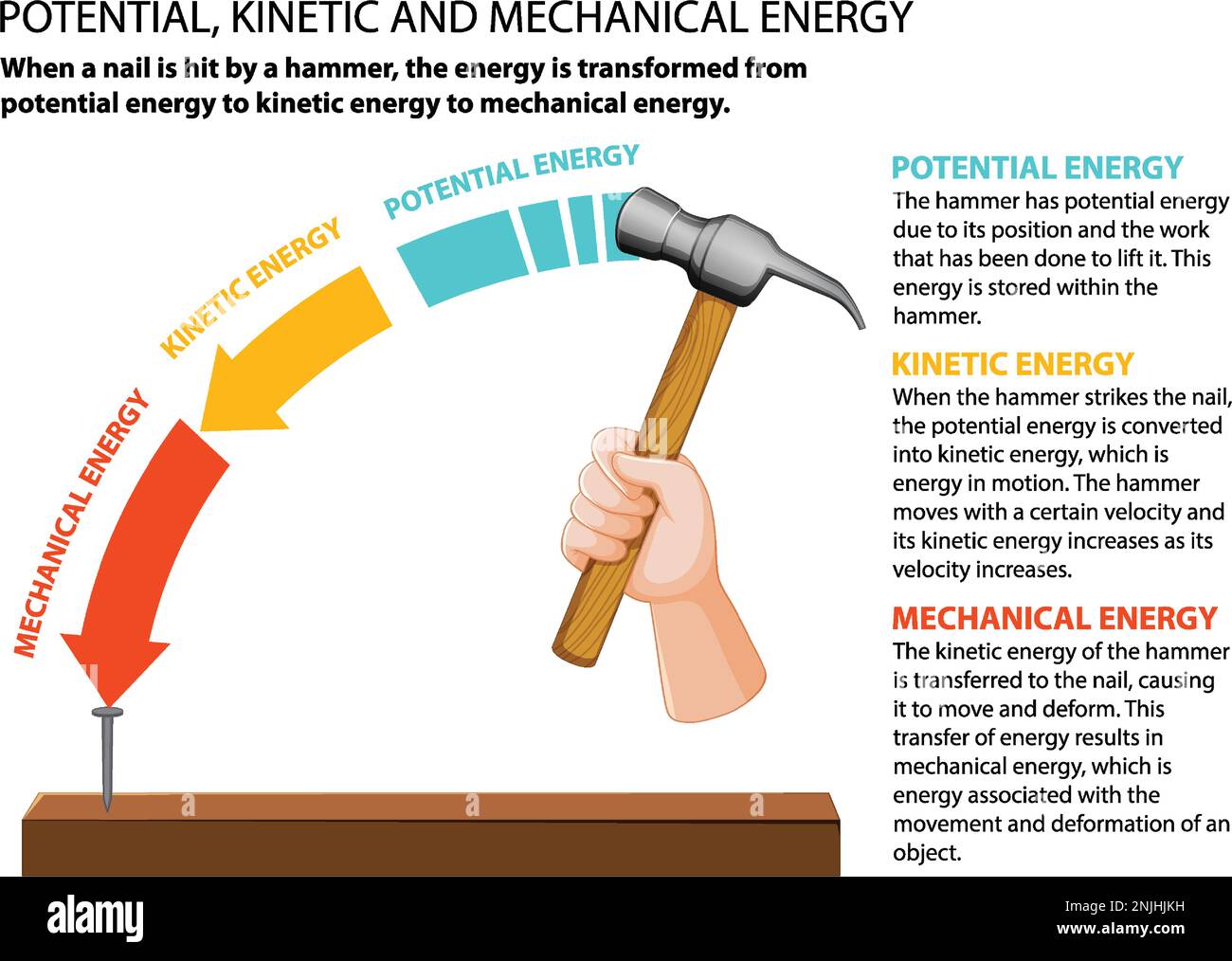
- Ballistic Missiles: These represent the "kinetic hammer." Traveling at hypersonic speeds during re-entry, they require advanced exo-atmospheric interception. The primary challenge here is not just speed but the "discrimination problem"—the ability of a radar to distinguish the warhead from the spent booster or decoys in a high-clutter environment.
The Failure of "Proxy Plausible Deniability"
For decades, the Middle East operated under a semi-stable equilibrium where Iran used regional affiliates—Hezbollah in Lebanon, the Houthis in Yemen, and various militias in Iraq—to exert pressure without triggering a direct conventional response. This "proxy shield" provided Tehran with strategic depth.
The shift to direct strikes from Iranian soil signifies a breakdown of this insulation. When a state moves from "managed instability" via proxies to "direct kinetic projection," it signals that the perceived cost of inaction has surpassed the risk of total war. This transition fundamentally alters the intelligence requirements for regional actors; tactical warning times have shrunk from days (monitoring proxy movements) to minutes (monitoring silo hatches and fueling telemetry).
The Technical Constraints of Integrated Air Defense (IAD)
Israel’s defense is often characterized as "impenetrable," but no system is immune to the "leakage rate" inherent in high-volume salvos. In any complex air defense environment, three constraints dictate the outcome:
Sensor Saturation
Radars have a finite capacity for the number of tracks they can process and engage simultaneously. Modern AESA (Active Electronically Scanned Array) radars are highly capable, but a coordinated attack from multiple vectors (360-degree threat) forces a division of resources that can create "seams" in the coverage.
Magazine Depth
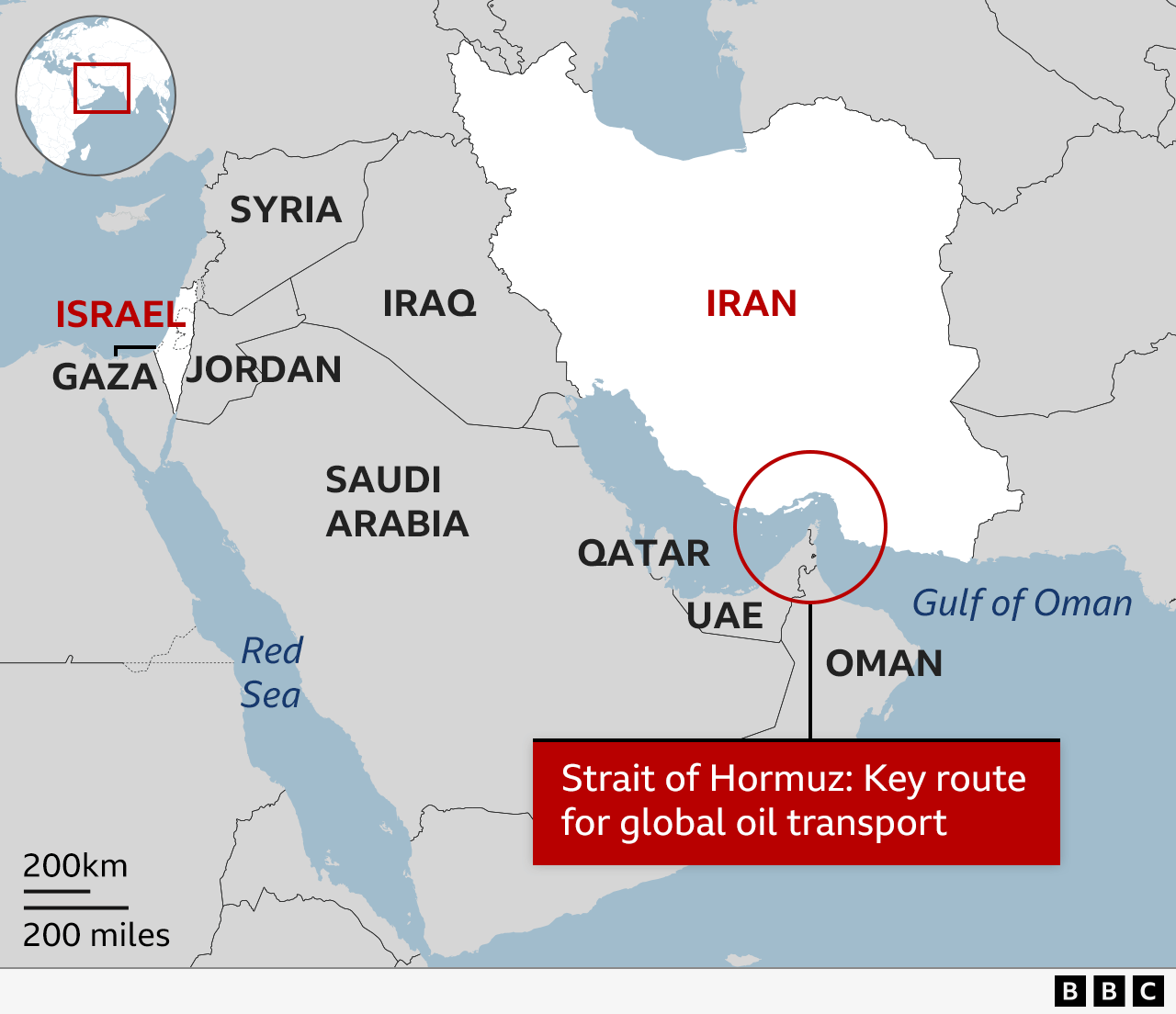
The most sophisticated defense system is a paperweight once its interceptor cells are empty. The logistics of re-arming a vertical launch system (VLS) or a mobile battery in the midst of a multi-wave attack is a vulnerability that state actors exploit. The geography of the Middle East—where flight times for ballistic missiles from Iran to Israel are roughly 10 to 12 minutes—leaves zero margin for logistical error.
The Problem of Debris
Interception is not disappearance. When a high-velocity ballistic missile is neutralized at 30,000 feet, the resulting debris field covers several square kilometers. Kinetic energy does not vanish; it is redistributed. Therefore, "successful" interceptions over populated areas can still result in significant ground-level casualties and infrastructure damage, which can be politically framed as a "hit" by the attacker.
Cyber-Kinetic Convergence: The Invisible Front
Modern missile warfare does not happen in a vacuum of physical trajectories. It is preceded and accompanied by a digital struggle for "electronic supremacy." Before a single drone is launched, electronic warfare (EW) units attempt to spoof GPS signals (GNSS jamming) to degrade the guidance systems of incoming threats.
Conversely, offensive actors utilize cyber operations to target the Command and Control (C2) nodes of the defense network. If the data link between a radar in the Negev and a battery in Galilee is disrupted for even sixty seconds, the defensive window closes. The recent exchanges have seen unprecedented levels of GPS interference across the Eastern Mediterranean, affecting civilian aviation—a clear indicator that the "electronic battlefield" is being fully utilized.
Structural Vulnerabilities in Regional Energy Grids
While the focus remains on military assets, the true strategic vulnerability lies in the energy and desalination infrastructure. The Middle East’s reliance on centralized power plants and water treatment facilities creates high-value, "brittle" targets.
- Refinery Vulnerability: Unlike military bunkers, oil refineries and gas processing plants are "soft" targets. A single drone strike on a distillation column can cause months of economic downtime.
- The Desalination Bottleneck: In arid regions, water security is tied directly to electricity. Targeting the power grid is, by extension, a strike against the water supply.
This creates a "Targeting Paradox." If Israel or Iran strikes the other's energy infrastructure, it invites a reciprocal strike that could collapse the domestic stability of both nations. Thus, we see a focus on military-to-military targets to maintain a rung on the "escalation ladder" that stops short of total societal collapse.
The Geopolitical Friction of Overflight Rights
The geography of an Iran-Israel conflict necessitates the violation of the sovereign airspace of third parties, primarily Jordan, Iraq, and Saudi Arabia. This transforms a bilateral conflict into a multilateral diplomatic crisis.
The participation of regional and international partners (such as the US, UK, and France) in intercepting Iranian assets over third-party territory creates a "defensive coalition" that Iran must factor into its strike calculations. However, this coalition is fragile. It relies on the premise that actions are purely defensive. If the conflict shifts to offensive operations launched from or through these third-party territories, the coalition risks fracturing due to internal political pressures within the Arab states.
Determining the "Last Clear Chance" for De-escalation
The current state of affairs is a "feedback loop of retaliation." In game theory, this is a classic "Prisoner's Dilemma" played at scale. Both parties would benefit from a return to the status quo, but neither can afford the perceived weakness of not responding to the last strike.
The mechanism for de-escalation is not found in "calls for restraint" but in the establishment of a new, mutually understood "Cost of Entry" for future attacks. This requires:
- Hardened Communication Channels: The use of intermediaries (e.g., Switzerland or Oman) to define the boundaries of "acceptable" targets.
- Proportionality Calibration: Ensuring that a response does not exceed the "kinetic weight" of the provocation, thereby allowing the opponent to "absorb" the blow without further escalation.
The limitation of this strategy is that it assumes rational actors with perfect control over their internal hardline factions. In a high-friction environment, a single technical malfunction—a missile off-course hitting a high-casualty civilian target—can bypass all structural safeguards and trigger a full-scale regional war.
The strategic play is no longer about "winning" a war that has no clear territorial objective. Instead, it is an exercise in "Escalation Management." Success is defined by the ability to project enough power to deter the opponent while maintaining enough restraint to prevent a total systemic collapse. The transition from shadow war to direct exchange has removed the safety net of plausible deniability, leaving both nations on a narrow path where the margin for error is measured in centimeters of radar accuracy and seconds of decision-making time.
Would you like me to analyze the specific technical specifications of the current interceptor stockpiles in the region to assess the projected duration of a high-intensity conflict?