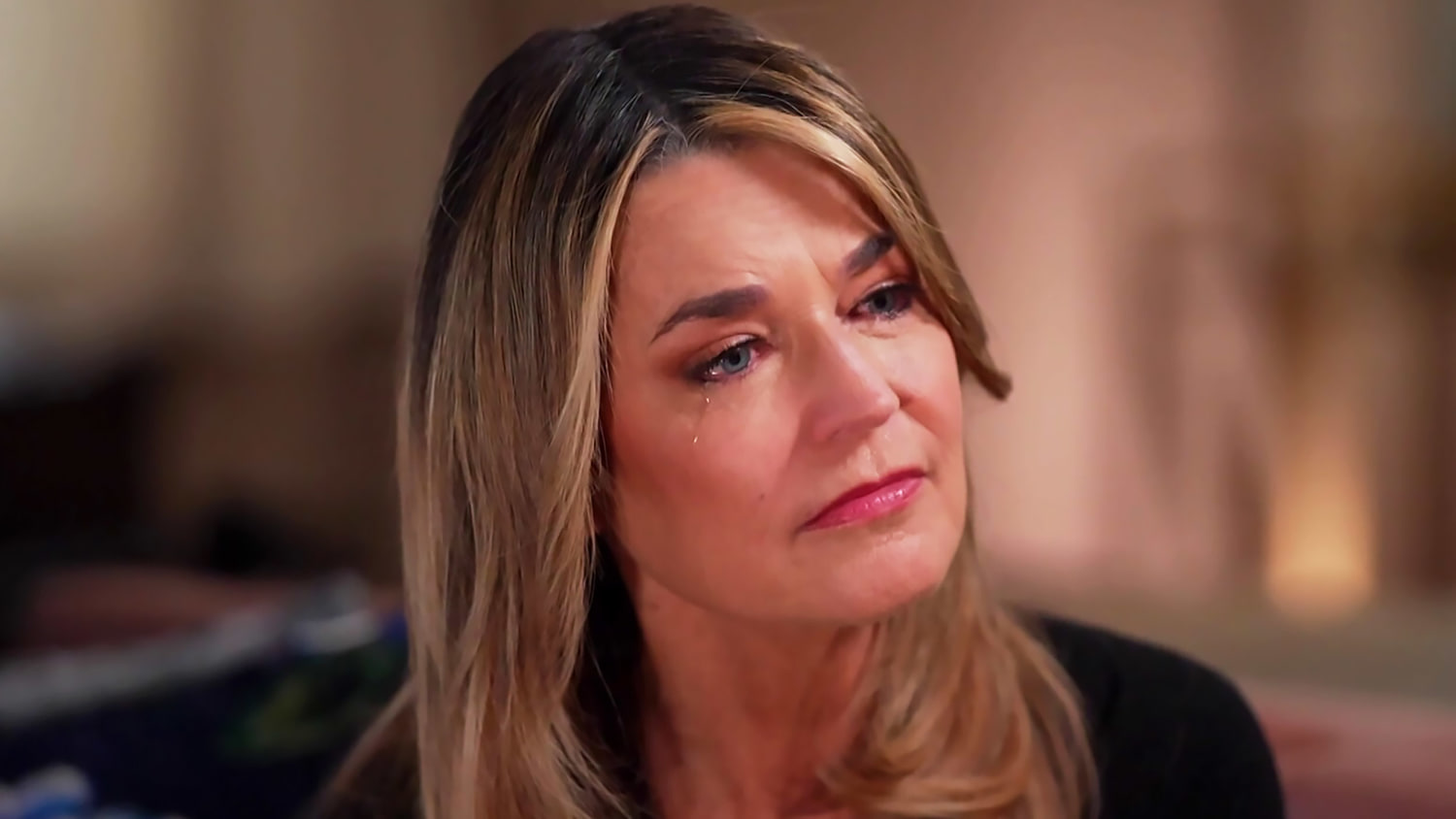
When Savannah Guthrie’s mother, Nancy, became the target of a sophisticated scam, it wasn't just a lapse in digital security. It was a calculated exploitation of a public figure's greatest vulnerability—their family. For decades, the trade-off for a seat at the anchor desk or a starring role was a loss of personal privacy. Today, that trade-off has morphed into a direct security threat. The "Today" show co-anchor recently shared the chilling realization that her mother may have been singled out specifically because of her daughter’s fame. This isn't an isolated incident of elder fraud. It is the new frontline of targeted criminal social engineering.
Criminals no longer cast wide nets with poorly spelled emails. They use open-source intelligence to map out the relatives of the wealthy and the visible. By the time a phone call is placed, the attacker often knows the victim’s address, their children’s names, and their travel schedules. In Nancy Guthrie’s case, the scammer posed as a representative from a tech giant, claiming her accounts were compromised. While the attempt failed, the psychological residue remains. It highlights a brutal reality. Being a household name now puts a target on the backs of those you love most.
The Architecture of a Targeted Scam
The mechanics of these attacks have evolved far beyond simple "phishing." We are seeing the rise of "whaling" operations that trick people into giving up massive sums or sensitive access. When a celebrity is involved, the motive is twofold. First, there is the assumption of deep pockets. Second, there is the leverage. If a scammer can convince a parent that their famous child is in legal trouble or financial peril, the emotional response overrides logical defenses.
Data brokers sell the building blocks for these crimes. For a few dollars, anyone can access records that link family members across generations. This data is then cross-referenced with social media activity. If a celebrity posts a birthday tribute to their mother, a scammer now has a name, a face, and a timeline. They wait for the celebrity to be "on assignment" or traveling—information easily found via a quick search of news cycles—and then they strike the vulnerable relative. They know the celebrity is unreachable, making the scam harder to verify.
The Social Engineering Factor
Scammers are talented actors. They don't just read a script; they build a narrative. In the Guthrie case, the pressure was immediate. They create a sense of frantic urgency. This is a physiological tactic designed to trigger a "fight or flight" response in the brain. When the brain is in this state, the prefrontal cortex—the part responsible for rational decision-making—effectively shuts down.
Criminals often use "spoofing" technology to make the caller ID display a trusted name, like a local police department or a bank. For an older victim, seeing a legitimate-looking number is often the only proof they need. They aren't looking for a digital signature. They are looking at a screen that says "Security Department."
The Security Gap in the Media Industry
Major networks like NBC, ABC, and CBS have massive security budgets, but those funds are almost exclusively directed at the talent and the physical studios. There is a glaring lack of support for the extended families of these public figures. While an anchor might have a security detail at a public event, their retired parents in a different state are often left to navigate the digital world with no more protection than the average person.
This is a failure of duty of care. If a journalist’s work makes their family a target, the employer should arguably provide the resources to harden those secondary targets. This includes specialized identity theft protection, private data removal services, and regular security briefings for family members. We are seeing a shift where talent contracts are beginning to include "family digital protection clauses," but it is not yet the industry standard. It needs to be.
Why the Legal System is Failing Victims
The current legal framework is woefully equipped to handle international cybercrime syndicates. When Nancy Guthrie is targeted, the person on the other end of the line is likely thousands of miles away, operating out of a "scam factory" in a jurisdiction that does not cooperate with U.S. law enforcement.
Local police departments often lack the forensic tools or the jurisdiction to pursue these cases. They provide a report for insurance purposes and little else. This creates a culture of impunity for the scammers. They know the risk of prosecution is near zero. They also know that celebrities are often hesitant to go public with these stories because of the "Streisand Effect"—drawing more attention to their family’s vulnerability. Guthrie’s decision to speak out is a rare break from that silence, intended to warn others, but it also underscores how defenseless even the most connected people truly are.
The Psychological Toll of Visibility
The fear Guthrie expressed—that her success caused her mother’s distress—is a specific kind of "survivor’s guilt" prevalent in the public eye. It changes how these individuals interact with the world. It leads to self-censorship and a retreat from the public square. When your career choices jeopardize your parents' safety, the cost of that career becomes astronomical.
This isn't just about money. It’s about the erosion of the private sphere. If you cannot call your mother without wondering if she’s been harassed by someone using your name as a weapon, the quality of life for the high-profile individual collapses. The industry treats this as a "personal problem," but it is a systemic byproduct of the fame machine.
Tactical Defenses for the High Profile
Relying on big tech or the government to solve this is a losing strategy. Protection must be proactive and manual. High-profile families are moving toward "analog" verification methods.
- The Family Password: A simple, unguessable word or phrase that must be spoken to verify any emergency. If the caller doesn't know the word, the conversation ends.
- Data Scrubbing: Using professional services to aggressively remove home addresses and phone numbers from "people search" sites.
- Hardware Security Keys: Moving away from SMS-based two-factor authentication, which is easily bypassed by SIM-swapping, and using physical keys like YubiKeys.
- The "Call Back" Rule: Never engaging with an inbound call. Hanging up and calling the known, official number of the institution claiming to reach out.
These steps are tedious. They are inconvenient. But in an era where deepfake audio can now mimic a child’s voice with terrifying accuracy, they are the only hurdles that actually work.
The Future of Targeted Extortion
We are entering a phase where AI will make these attacks indistinguishable from reality. We’ve already seen cases where AI-generated voice clones were used to demand ransom from parents, convincing them their child had been kidnapped. For a celebrity whose voice is recorded and available in thousands of hours of high-quality digital audio, the risk is exponential. A scammer can train a model on a journalist's nightly broadcasts and call their parents using a voice that is tonally perfect.
The Guthrie incident is a canary in the coal mine. It signals that the "public" part of a public figure's life is being indexed and weaponized in ways we are only beginning to understand. The barrier between professional visibility and private safety hasn't just been breached; it has been demolished. Protecting the family is no longer a secondary concern. It is the primary security challenge of the next decade.
Families must realize that their digital footprint is a map for predators. Every tagged photo and every "check-in" is a data point. For those in the spotlight, the only way to protect the people they love is to become digitally invisible—a task that is becoming nearly impossible in a world that demands constant connectivity.
The responsibility now falls on the individual to build their own fortress. Wait for no one to save you.
Would you like me to draft a specific "Digital Hardening Checklist" for high-profile families to give to their relatives?